DNS: The First Step of Almost Every Internet Connection
The Domain Name System (DNS) is responsible for translating
human-readable domain names into IP addresses used by computers.
Before a user can visit a website, send an email, download software,
or connect to a cloud service, their device must first resolve a domain name
through DNS.
This means DNS sits at the beginning of almost every Internet interaction:
- Web browsing
- Email delivery
- API communication
- Software updates
- Cloud service connections
Because DNS resolution occurs before the actual network connection,
it provides a strategic point where security systems can
observe, detect, and block malicious activity.
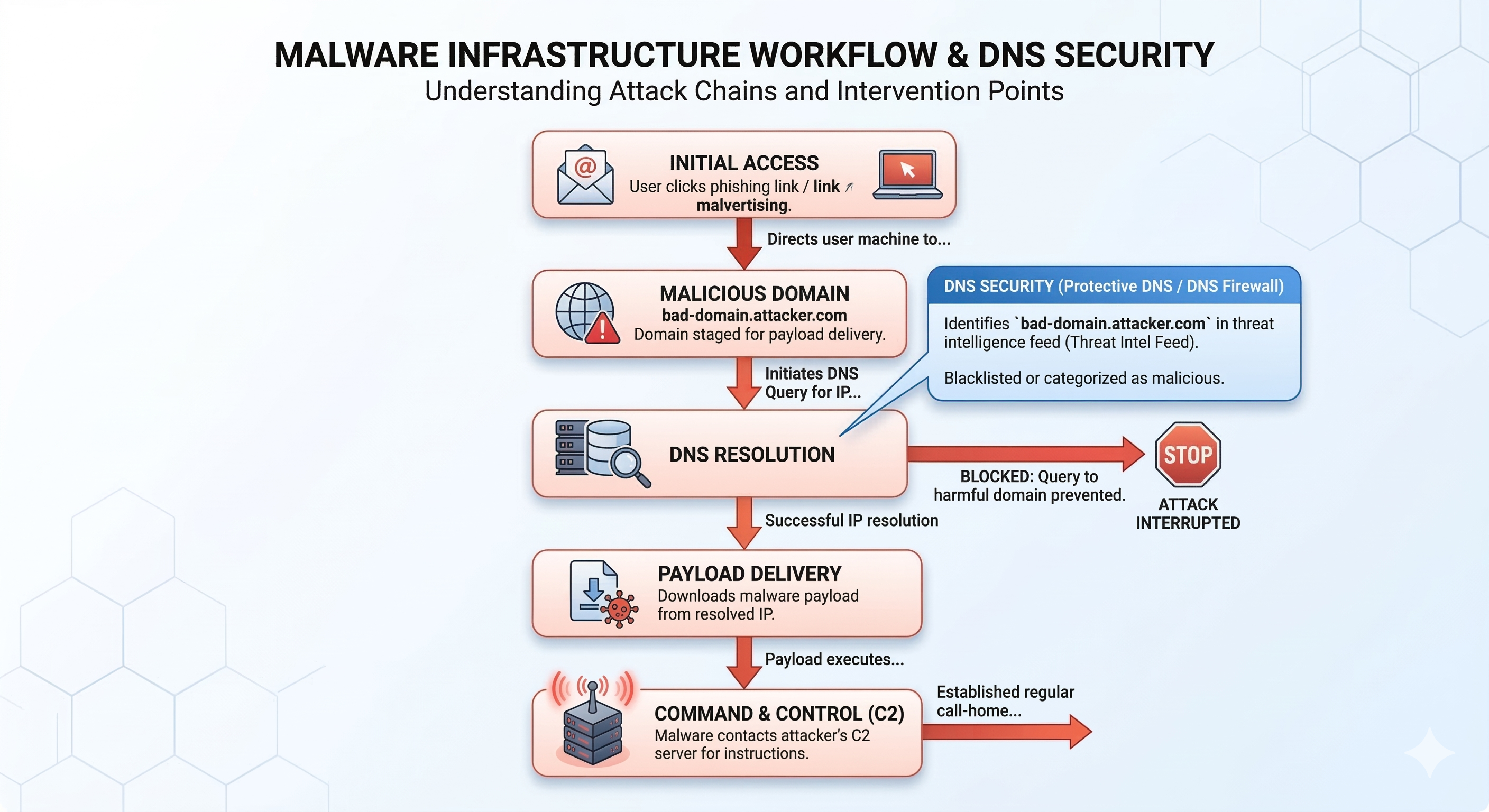
Why Attackers Use DNS Infrastructure
Many cyberattacks rely on DNS infrastructure to locate malicious servers,
deliver malware payloads, and maintain command-and-control communication.
DNS firewalls and Protective DNS systems can stop these attacks during the
DNS resolution stage.
Cybercriminals rely heavily on DNS to operate their infrastructure.
Malware and phishing campaigns typically depend on domain names
to locate servers that host malicious payloads or control infected devices.
Common attack scenarios include:
- Phishing domains used to impersonate legitimate websites
- Malware distribution servers hosting infected downloads
- Botnet command-and-control servers
- Domain Generation Algorithms (DGA) used by malware
- Traffic Distribution Systems (TDS) redirecting victims
Many modern attacks involve large networks of domains that are
rapidly created and abandoned to evade detection.
More detailed examples of these attack infrastructures can be found in
How Malware Uses DNS and
Malware Domains and DNS Attack Infrastructure.
DNS as an Early Detection Point
Because DNS queries occur before most network connections,
DNS traffic provides valuable visibility into potential security incidents.
Security monitoring systems often analyze DNS queries to detect:
- Infected devices contacting botnet infrastructure
- Lookups to newly registered suspicious domains
- Domain generation algorithm patterns
- Connections to known malware infrastructure
This makes DNS telemetry an important data source for
Security Operations Centers (SOC),
threat intelligence platforms, and incident response teams.
How DNS Security Technologies Stop Attacks
Several technologies have been developed to improve DNS security
and prevent attackers from abusing DNS infrastructure.
These mechanisms allow DNS infrastructure to stop attacks
before connections to malicious servers occur.
Why Enterprises and ISPs Deploy DNS Security
Because DNS is such a central component of Internet communication,
organizations increasingly deploy DNS security platforms
as part of their cybersecurity architecture.
Typical deployments include:
- Enterprise security monitoring platforms
- Government protective DNS programs
- Internet Service Provider malware filtering
- Managed Security Service Providers (MSSPs)
By filtering malicious domains at the DNS layer,
these systems can prevent malware infections,
block phishing attacks, and disrupt botnet activity
across entire networks.
Related DNS Security Topics
This article is part of the DNS Security and Infrastructure Guide, a knowledge base covering DNS resolution, DNSSEC, encrypted DNS, Protective DNS filtering, and DNS infrastructure.