What is Protective DNS?
#
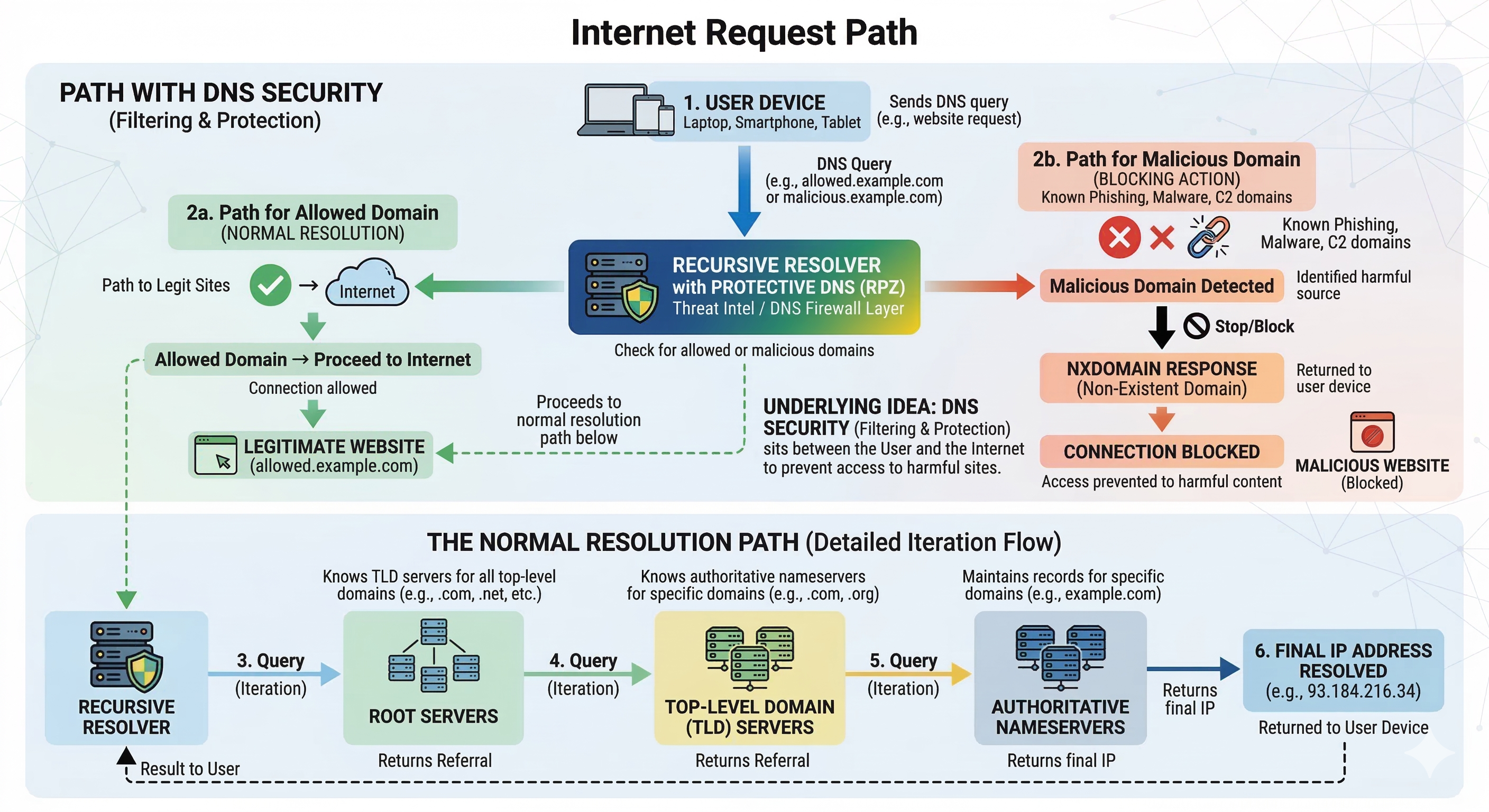
Protective DNS is a cybersecurity technique that prevents users and devices
from connecting to malicious domains during the DNS resolution process.
Instead of allowing DNS queries to resolve normally, a Protective DNS resolver
applies security policies that block domains associated with malware,
phishing campaigns, botnets and other cyber threats.
Because almost every Internet connection begins with a DNS lookup,
DNS infrastructure provides a powerful control point for preventing
connections to dangerous systems across the Internet.
Protective DNS solutions are commonly deployed by:
- Enterprise corporate networks
- Government and defense environments
- Educational institutions
- Internet Service Providers
- Managed Security Service Providers
How Protective DNS Works
#
When a device attempts to connect to a domain, the DNS resolver
checks the request against threat intelligence databases that contain
domains associated with cybercrime infrastructure.
If the queried domain appears in a threat intelligence feed,
the DNS resolver can apply a security action such as:
- Return NXDOMAIN (pretend the domain does not exist)
- Return NODATA
- Redirect the request to a security warning page
- Log the event for security monitoring
These actions prevent infected machines or unsuspecting users
from connecting to attacker infrastructure.
Protective DNS as a DNS Firewall
#
Protective DNS is often described as a DNS firewall.
Just as traditional firewalls control network traffic based on
IP addresses and ports, DNS firewalls enforce security policies
during DNS resolution.
Technologies such as Response Policy Zones (RPZ) allow DNS
resolvers to override normal DNS responses and apply security policies
based on threat intelligence feeds.
This makes DNS an effective layer for blocking threats including:
- Malware distribution domains
- Phishing websites
- Botnet command-and-control infrastructure
- Cryptomining malware
- Fraud and scam websites
Why Internet Service Providers Deploy Protective DNS
#
Internet Service Providers face increasing pressure to protect the
reputation of their IP address space and reduce abusive traffic
originating from infected customer devices.
Without DNS filtering, users may unknowingly access malicious domains
through phishing campaigns, compromised websites or malicious
advertising networks.
Once infected, these devices may participate in malicious activity
such as:
- Brute-force attacks against SSH, RDP or email services
- Scanning the Internet for vulnerable systems
- Sending spam directly via SMTP
- Connecting to botnet command-and-control infrastructure
These activities frequently cause ISP IP addresses to appear in
reputation systems such as:
- Spamhaus
- Cisco Talos Intelligence
- SORBS
- AbuseIPDB
Deploying Protective DNS significantly reduces malware infections
and outbound abuse traffic, helping ISPs protect the reputation
of their networks.
Threat Intelligence Feeds
#
Protective DNS relies heavily on continuously updated
threat intelligence feeds.
These feeds contain indicators of compromise such as
malicious domains, botnet command-and-control servers
and phishing infrastructure discovered by security
research organizations.
Threat intelligence sources may include:
- Malware analysis platforms
- Phishing detection systems
- Botnet tracking infrastructure
- Commercial cybersecurity intelligence providers
These feeds are frequently converted into DNS policy
zones used by DNS firewalls.
Why DNS is a Strategic Security Layer
#
DNS sits at a strategic location in the Internet architecture.
Before a browser, application or device connects to a server,
it must first resolve the domain name to an IP address.
Because of this, DNS infrastructure can act as an early
security checkpoint capable of blocking many threats
before network connections are established.
This approach provides several advantages:
- Protects entire networks without installing endpoint software
- Blocks threats before connections occur
- Provides visibility into malicious domain activity
- Scales easily for very large networks
Related DNS Security Topics