Current reality of SNI visibility in TLS 1.3
#
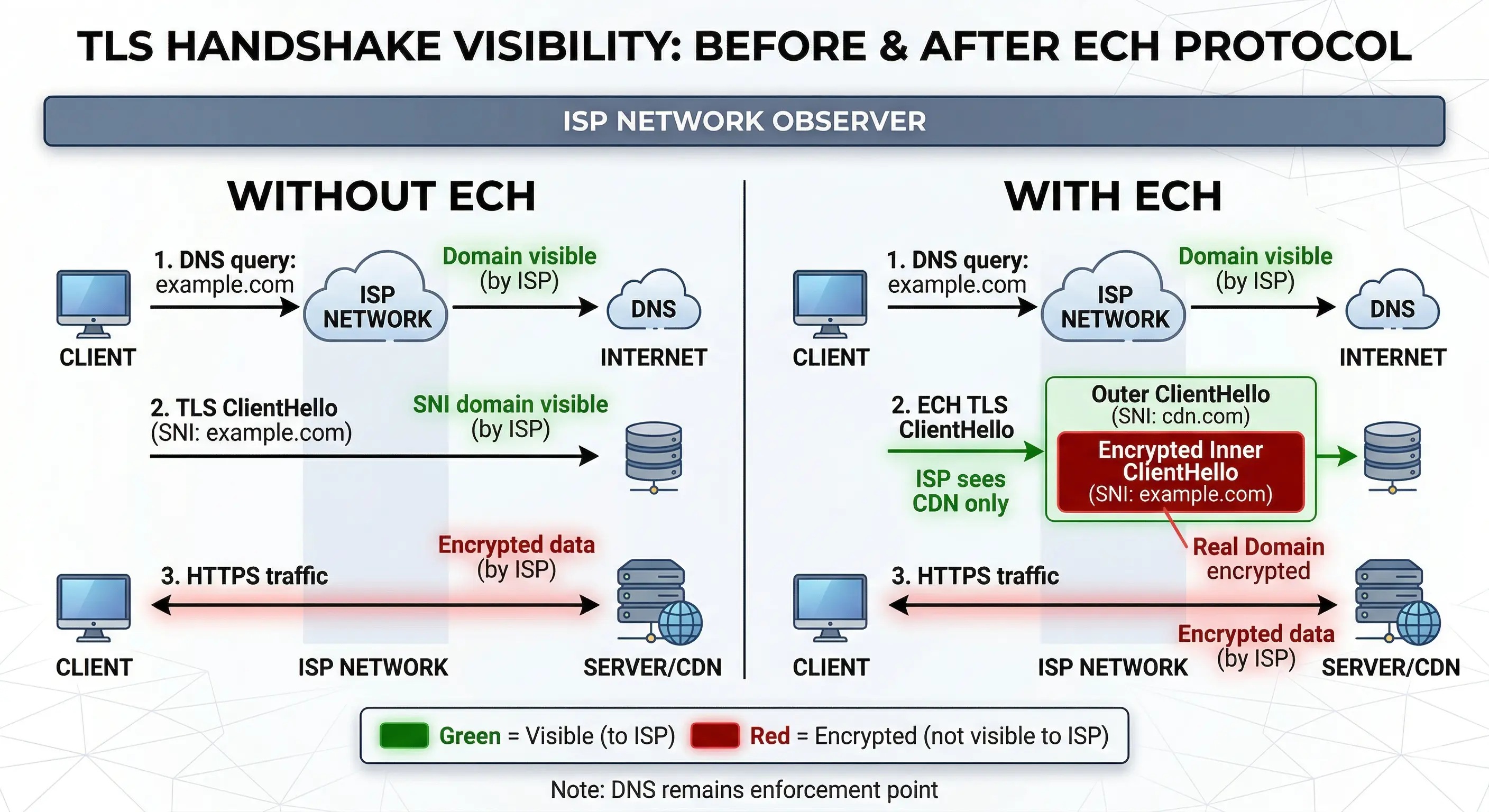
A common misconception is that TLS 1.3 encrypts all connection
metadata. While TLS 1.3 encrypts certificates and application data,
the initial ClientHello message remains visible to the network.
This includes the Server Name Indication (SNI) field, which reveals
the hostname a client is attempting to reach.
This behavior can be easily demonstrated with standard packet
capture tools available on any Linux system.
Demonstrating SNI visibility with tshark
The following command extracts both DNS queries and TLS SNI values
from live traffic:
tshark -i any \
-Y "dns.qry.name or tls.handshake.extensions_server_name" \
-T fields \
-e frame.time \
-e dns.qry.name \
-e tls.handshake.extensions_server_name
This allows operators to directly observe how DNS resolution and
TLS hostname disclosure correlate during normal browsing activity.
Generating a TLS 1.3 connection
A simple curl request is sufficient to trigger a TLS handshake:
curl --tlsv1.3 https://www.planisys.net > /dev/null
Example tshark output
A typical capture may look like:
10:41:22 www.planisys.net
10:41:22 www.planisys.net
The first line corresponds to the DNS query.
The second line corresponds to the TLS ClientHello SNI field.
This demonstrates that the requested hostname is visible twice in
a normal connection workflow.
Operational security implication
Even with TLS 1.3, the ClientHello remains visible. A simple packet
capture demonstrates that the requested hostname is transmitted in
cleartext unless ECH is enabled.
This visibility allows passive observers on shared networks such as
public Wi-Fi environments to determine which domains users are
accessing, even though the encrypted HTTPS content itself remains
protected.
Why this matters
Historically, this visibility enabled network operators to perform:
- Traffic classification
- Security investigations
- Malware detection
- Abuse correlation
- Incident response analysis
ECH specifically targets this remaining metadata exposure by encrypting
the ClientHello hostname while preserving TLS security guarantees.
What a passive eavesdropper can observe today
In a typical public Wi-Fi environment such as a hotel, airport or café,
a passive observer with packet capture capability does not need to
break encryption to learn meaningful information about user activity.
Because the TLS ClientHello and DNS queries remain visible, an
observer can still extract valuable metadata.
Using standard tools such as tcpdump or tshark, an eavesdropper may
be able to determine:
- Which websites a user connects to
- When connections occur
- Connection frequency and timing patterns
- Which cloud providers or platforms are used
- Which email providers are accessed
- Which messaging platforms are used
- Which banking or SaaS platforms are contacted
Even without access to encrypted content, this metadata can allow
behavioral profiling. For example, repeated connections to specific
services may reveal professional activity, technology usage patterns
or organizational relationships.
This type of analysis is known as traffic metadata analysis
and has historically been used both for network troubleshooting and
security monitoring, but it also represents a privacy concern in
untrusted network environments.
What remains protected even without ECH
It is important to note that HTTPS and TLS 1.3 still protect the
confidentiality and integrity of the session itself. A passive
observer cannot see:
- Passwords
- Cookies
- Page content
- Form submissions
- Email contents
- Downloaded files
ECH therefore does not replace TLS encryption, but rather extends it
by protecting the remaining hostname metadata exposed during the
initial connection phase.
What large-scale network monitoring systems can still infer
Beyond simple packet capture, large network operators such as ISPs,
enterprises and cloud providers often use flow telemetry platforms
based on NetFlow, IPFIX or sFlow to understand network behavior at
scale. These systems do not inspect encrypted payloads but instead
analyze connection metadata.
Even without decrypting traffic, operators can often combine multiple
signals such as:
- DNS queries
- TLS SNI values
- Destination IP addresses
- Autonomous System destinations
- TLS fingerprinting (JA3/JA4)
- Connection timing patterns
- Traffic volume characteristics
When correlated together, these signals can provide a fairly accurate
understanding of the type of activity occurring on a network without
requiring access to encrypted content.
Typical operational uses of this visibility
In ISP environments this visibility has traditionally supported:
- Detection of infected customer devices
- Botnet activity identification
- Spam outbreak investigation
- Abuse complaint validation
- DDoS investigation
- Network capacity planning
- Security incident response
This type of monitoring is generally focused on infrastructure
protection rather than user inspection, particularly in regulated
telecommunications environments where operators are responsible
for mitigating abuse originating from their networks.
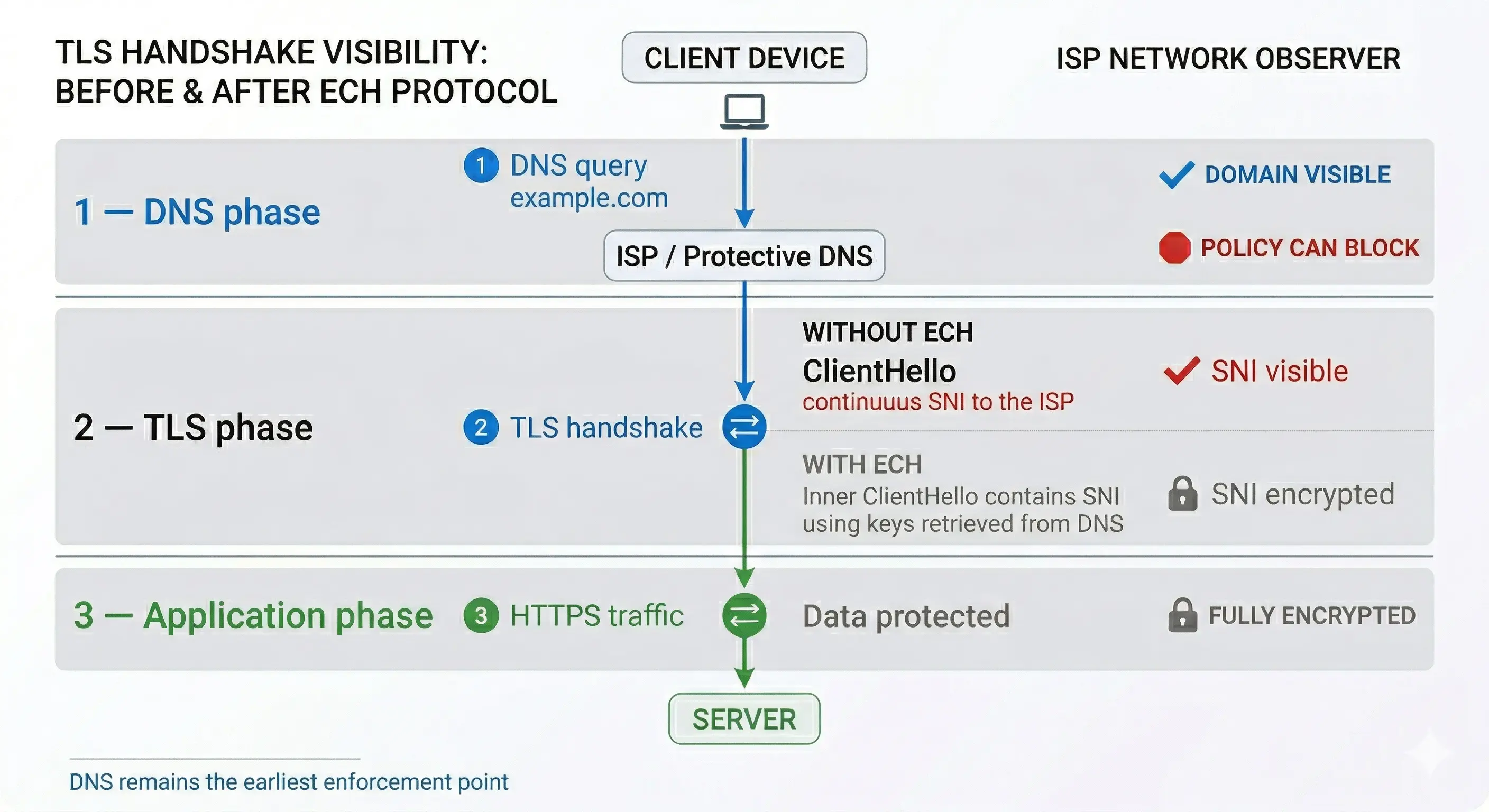
Why encryption is shifting the security control point
As technologies such as TLS 1.3, QUIC and ECH progressively reduce
the visibility of transport and session metadata, traditional
network traffic inspection becomes less reliable as a primary
security mechanism.
This architectural evolution is one of the reasons why many operators
are moving toward earlier control points in the connection lifecycle,
particularly DNS-based prevention and endpoint security, rather than
relying on post-connection inspection.
From an operational standpoint, this reinforces the role of DNS as one
of the earliest observable events in most Internet connections.
Operator reality: the Internet is becoming opaque
Over the past decade, Internet protocols have evolved toward encrypting not only data, but also metadata.
For DNS operators and ISPs this represents a fundamental architectural shift.
Security detection historically relied on multiple visibility layers:
- DNS queries
- TLS SNI hostname
- HTTP host headers
- Traffic fingerprints
- Flow telemetry
Modern protocol evolution is systematically removing these signals.
The visibility layers disappearing
| Technology |
What it hides |
| HTTPS |
Application content |
| TLS 1.3 |
Handshake metadata |
| DoH / DoT |
DNS queries |
| QUIC |
Transport patterns |
| ECH |
Requested hostname |
The cumulative effect is clear:
Network inspection is becoming unreliable as a security strategy.
Modern encryption technologies such as TLS 1.3, QUIC and ECH reduce network inspection capabilities. DNS remains one of the earliest enforcement points available to security operators.
ECH security motivation: strong privacy goals vs operational DNS reality
#
Encrypted Client Hello (ECH) was introduced to address a legitimate privacy limitation in TLS.
Even after the adoption of HTTPS, the Server Name Indication (SNI) field remained visible in plaintext, allowing passive observers to determine which websites users were visiting.
The IETF draft on deployment considerations provides an operational overview of this motivation:
ECH Deployment Considerations – IETF Draft
From a protocol design perspective, ECH represents a significant improvement in Internet privacy because it closes one of the last remaining metadata leaks in TLS connections.
The legitimate privacy problems ECH addresses
ECH primarily protects users against environments where network traffic may be monitored by third parties.
Examples include:
- Public Wi-Fi networks
- Hotel networks
- Airport networks
- University networks
- Shared corporate networks
- Countries performing traffic surveillance
- Hostile or untrusted network operators
In these environments, preventing hostname visibility provides real privacy benefits.
ECH significantly reduces the ability of passive observers to build browsing profiles based on TLS metadata.
Different threat model in ISP recursive DNS environments
The operational environment of ISP recursive DNS platforms is fundamentally different from these threat models.
ISP DNS resolvers typically operate:
- Inside the ISP network
- Restricted to ISP address space
- Serving only subscriber networks
- Under regulatory obligations
- With abuse mitigation responsibilities
- Focused on malware prevention
In this context, DNS filtering through RPZ is not designed for traffic inspection or user profiling.
Its primary purpose is infrastructure protection and threat prevention.
The real operational goal of ISP DNS security
In practice, large ISP recursive DNS platforms primarily use DNS security to:
- Block malware command and control domains
- Reduce botnet activity
- Prevent phishing infections
- Reduce spam originating from infected customers
- Protect IP reputation
- Lower abuse complaints
These protections operate at the domain reputation level rather than through traffic inspection.
ECH does not affect these capabilities because DNS enforcement occurs before TLS connections begin.
Where ECH makes the most sense
ECH provides the strongest benefits in environments where users cannot trust the network they are connected to.
This includes:
- Public access networks
- Shared infrastructure environments
- Countries with aggressive monitoring
- High-risk political environments
In these situations, encrypting TLS metadata is clearly beneficial.
Where DNS security remains critical
In ISP environments, the primary security concern is typically not passive observation of users, but active compromise of customer devices.
Infected endpoints generate malicious DNS traffic regardless of TLS privacy protections.
Operational DNS telemetry across large recursive platforms consistently shows that malware relies heavily on domain infrastructure:
- DGA domains
- Phishing domains
- C2 infrastructure
- Fast-flux hosting
- Malvertising domains
Blocking these domains prevents compromise regardless of whether TLS metadata is encrypted.
Privacy and DNS protection are not contradictory
ECH should not be seen as conflicting with Protective DNS.
They address different problems:
| Technology |
Primary goal |
| ECH |
Protect user privacy |
| Protective DNS |
Prevent compromise |
Both approaches can coexist because they operate at different layers.
ECH protects metadata confidentiality.
Protective DNS prevents malicious infrastructure access.
The practical takeaway for DNS operators
ECH represents a continuation of the Internet trend toward stronger encryption.
For DNS operators this reinforces an already clear direction:
Security must increasingly rely on intelligence-driven prevention rather than traffic inspection.
From an operational perspective, DNS remains one of the earliest and most scalable control points available for protecting large user populations.
The practical impact of ECH for DNS operators
ECH removes TLS hostname visibility which many operators used for:
- Malware investigation
- Abuse tracing
- Traffic classification
- Botnet detection
- Security correlation
This does not eliminate security — but it changes where security must happen.
Security enforcement must now move earlier in the connection lifecycle.
Why DNS becomes the last scalable control point
Regardless of encryption, attackers still require infrastructure:
- Domains
- DNS resolution
- C2 communication
- Phishing hosting
- Malware distribution
This creates an operational reality:
DNS remains one of the few enforcement layers that cannot be bypassed at scale.
Connection lifecycle reality
DNS resolution → required
TLS handshake → now encrypted
Application traffic → encrypted
If a malicious domain is blocked at DNS, the connection never begins.
ECH does not break Protective DNS
A common misunderstanding is that ECH reduces DNS security effectiveness.
Operationally this is incorrect.
DNS filtering occurs before TLS.
DNS query → blocked
No IP returned
No TLS connection possible
ECH irrelevant
Because DNS enforcement happens first, ECH does not affect:
- RPZ filtering
- Malware domain blocking
- Threat intelligence enforcement
- Phishing protection
- Botnet disruption
What actually becomes harder after ECH
ECH primarily affects operational workflows after DNS resolution:
- TLS traffic investigation
- Post-incident analysis
- Passive network monitoring
- Correlation workflows
- Traffic classification
For large ISPs this mainly impacts telemetry quality rather than prevention capability.
Why this matters especially for ISPs
Large ISP recursive DNS platforms continuously observe malware activity from infected customer devices.
Protective DNS often serves as the first containment mechanism.
Without DNS filtering, ISPs typically experience:
- Customers participating in botnets
- Spam originating from residential networks
- IP blacklist incidents
- Support complaints
- Abuse reports
- Reputation degradation
These operational realities explain why many ISPs deploy DNS security even when traffic inspection becomes ineffective.
The real strategic shift: prevention over inspection
ECH accelerates a broader industry transition:
Old model:
Inspect traffic → detect compromise
Emerging model:
Block infrastructure → prevent compromise
This shift favors DNS security because DNS operates before encryption begins.
Why Protective DNS becomes more important after ECH
As encryption removes inspection capability, organizations must rely more on prevention.
DNS becomes one of the few scalable prevention layers available.
Protective DNS helps by:
- Blocking malware domains
- Stopping command and control
- Preventing phishing resolution
- Reducing infections
- Lowering incident response costs
Observed operational benefits
Operators deploying Protective DNS commonly observe:
- Reduced abuse complaints
- Lower botnet traffic
- Improved IP reputation
- Reduced support workload
- Lower incident frequency
How DNS operators should adapt
Recommended operator strategy
- Invest in DNS intelligence feeds
- Strengthen RPZ deployment
- Increase DNS telemetry analysis
- Deploy anomaly detection
- Correlate DNS behavior patterns
- Focus on early threat disruption
The key lesson from ECH deployment discussions
The long-term trend is clear:
Security visibility will decrease.
DNS prevention will increase in importance.
Future security architecture
ECH reinforces an architectural direction already visible in modern networks:
- Zero trust models
- DNS security layers
- Endpoint detection
- Threat intelligence
- Behavioral monitoring
DNS remains one of the few control points that scales across ISPs, enterprises and cloud environments.
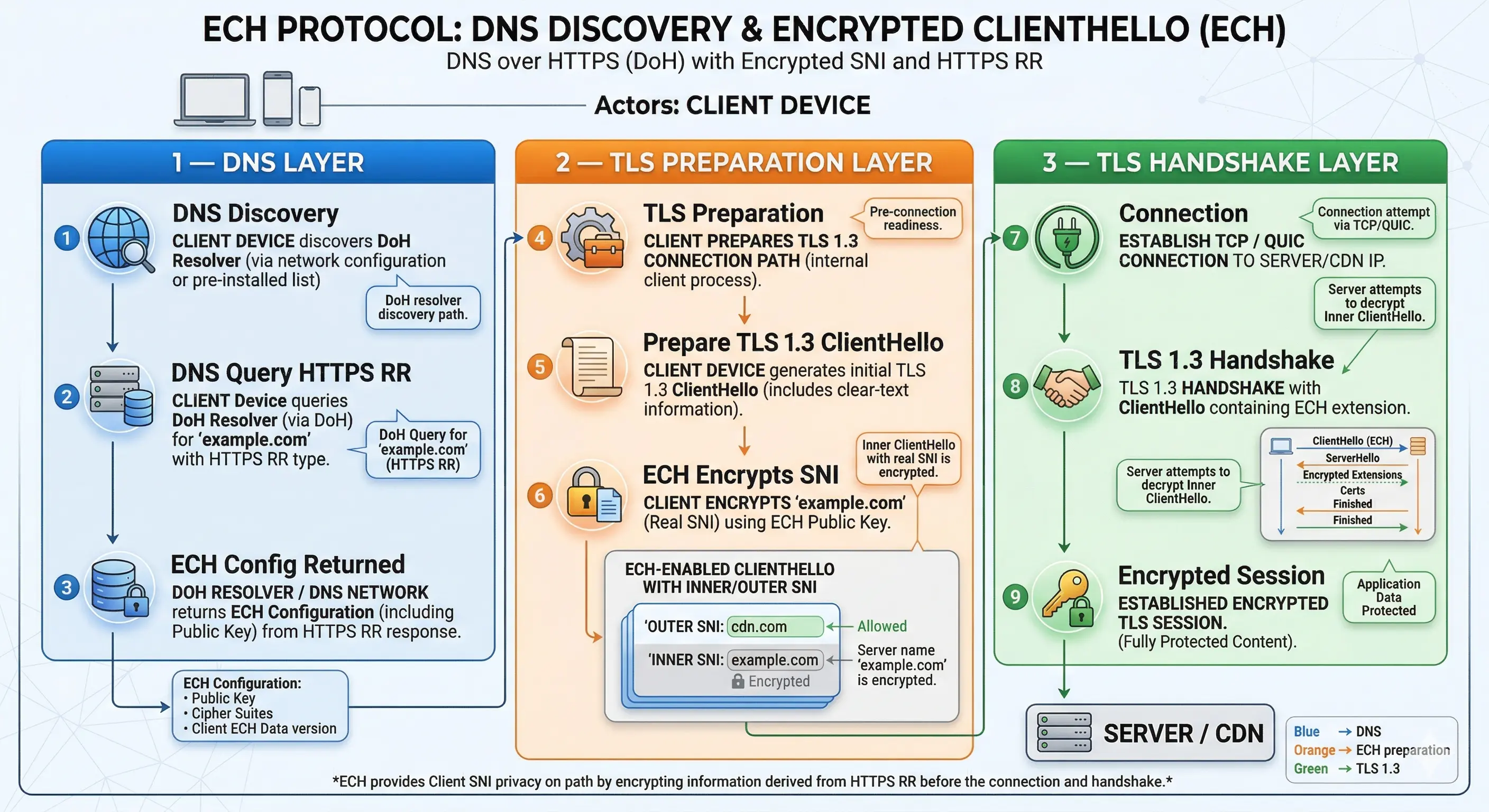
How ECH is deployed in practice
#
ECH deployment requires coordination between web infrastructure,
DNS publication and client support. Unlike traditional TLS features,
ECH depends on DNS discovery through HTTPS resource records defined
in RFC 9460.
DNS requirements
ECH requires publication of an HTTPS (SVCB) DNS record containing
the echconfig parameter.
example.com. 300 IN HTTPS 1 . alpn="h2,h3" echconfig="BASE64CONFIG"
If the HTTPS record is not present, clients automatically fall back
to standard TLS without ECH.
Browser deployment reality
ECH support is still evolving and currently depends heavily on browser
implementation choices.
In practice, ECH is most commonly enabled when browsers use encrypted
DNS resolvers such as DNS over HTTPS.
This is not a protocol requirement, but an implementation decision
intended to prevent DNS manipulation of ECH configuration data.
Current support status
- Firefox — most mature deployment
- Chromium — experimental rollout
- Edge — follows Chromium
- Safari — early support stages
Figure — DNS discovery and ECH TLS 1.3 handshake workflow
ECH encrypts the TLS hostname after DNS resolution. Because DNS queries occur before the TLS 1.3 handshake begins, DNS security controls such as RPZ filtering remain effective prevention points.
If any requirement is missing — DNS record, browser support or
server capability — the connection proceeds normally without ECH.
Practical lab: testing ECH in 10 minutes
Because ECH deployment is still evolving, the easiest way to observe it
is by using domains that already support it. Cloudflare operates one of
the largest public ECH deployments, making it ideal for testing.
This simple lab requires only dig and Firefox.
Step 1 — Check if a domain publishes ECH
Query the HTTPS record:
dig crypto.cloudflare.com HTTPS
Example output:
crypto.cloudflare.com. 300 IN HTTPS 1 .
alpn="h2,h3"
echconfig="AEj+DQBB..."
If the echconfig parameter is present, the domain supports ECH.
Step 2 — Verify using kdig (optional)
kdig crypto.cloudflare.com HTTPS
This sometimes shows the structure more clearly than dig.
Step 3 — Enable ECH in Firefox
Open:
about:config
Verify these settings:
network.dns.echconfig.enabled → true
network.trr.mode → 3
network.trr.uri → https://mozilla.cloudflare-dns.com/dns-query
Explanation:
- echconfig.enabled enables ECH processing
- TRR mode 3 forces DoH
- Cloudflare DoH supports ECH discovery
Step 4 — Confirm ECH is active
Visit:
https://crypto.cloudflare.com/cdn-cgi/trace
Look for:
sni=encrypted
If present, ECH is active.
Step 5 — Observe fallback behavior
Disable DoH:
network.trr.mode → 0
Reload the page.
ECH may now disappear depending on resolver behavior.
This demonstrates how current browser implementations often tie
ECH activation to encrypted DNS usage.
Step 6 — Observe DNS dependency
Test a domain without HTTPS records:
dig example.com HTTPS
Result:
(no HTTPS record)
ECH cannot activate without this record.
Current server and infrastructure support for ECH
ECH support on the server side is still emerging because it requires
deep integration in the TLS stack rather than simple web server
configuration.
Unlike HTTP features that can be enabled through reverse proxy
configuration, ECH operates inside the TLS handshake and therefore
depends on cryptographic libraries such as OpenSSL, BoringSSL or NSS.
This means that even if a web server supports TLS 1.3, it cannot
automatically support ECH unless the underlying TLS implementation
also supports it.
Open source web server support status
| Software |
ECH support status |
Notes |
| NGINX |
Early support emerging |
Requires experimental OpenSSL ECH branch or upcoming OpenSSL 4.0 |
| Apache |
Experimental work |
Dependent on TLS library support |
| HAProxy |
Early implementation work |
Still evolving |
| Caddy |
Experimental ecosystem support |
Depends on Go TLS developments |
| CDN platforms |
Most mature deployments |
Cloud providers currently lead adoption |
TLS library dependency
The main limiting factor for ECH deployment today is TLS library
support. Historically, most web servers depend on OpenSSL, which
only recently began adding ECH capabilities in development branches
and future major releases.
Because of this dependency, many real-world deployments currently
occur at large CDN providers that maintain their own TLS stacks
based on BoringSSL or similar implementations.
Operational deployment reality
Today, most ECH-enabled connections are terminated at large edge
platforms rather than origin servers. This reflects the operational
complexity of maintaining TLS infrastructure capable of supporting
ECH key rotation, DNS publication and fallback handling.
As TLS libraries mature and ECH support becomes part of mainstream
OpenSSL releases, broader adoption in self-hosted environments is
expected.
For now, operators evaluating ECH should consider it an emerging
capability rather than a universally available feature.
Operator takeaway
This simple test demonstrates three important operational realities:
- ECH depends on DNS HTTPS records
- ECH typically requires modern resolver behavior
- DNS remains part of the connection trust chain
Even with ECH enabled, DNS resolution remains the first required step
before any encrypted TLS connection can occur.
Frequently Asked Questions
Does ECH reduce DNS security?
No. DNS filtering continues working because it occurs before TLS connections begin.
Does ECH make DNS filtering more important?
Yes. As traffic inspection decreases, DNS becomes one of the earliest prevention points.
Is ECH bad for ISPs?
ECH improves privacy but requires ISPs to rely more on DNS intelligence instead of traffic inspection.
Related DNS Security Topics