DNSSEC, DoT, DoH and ADoT Explained
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
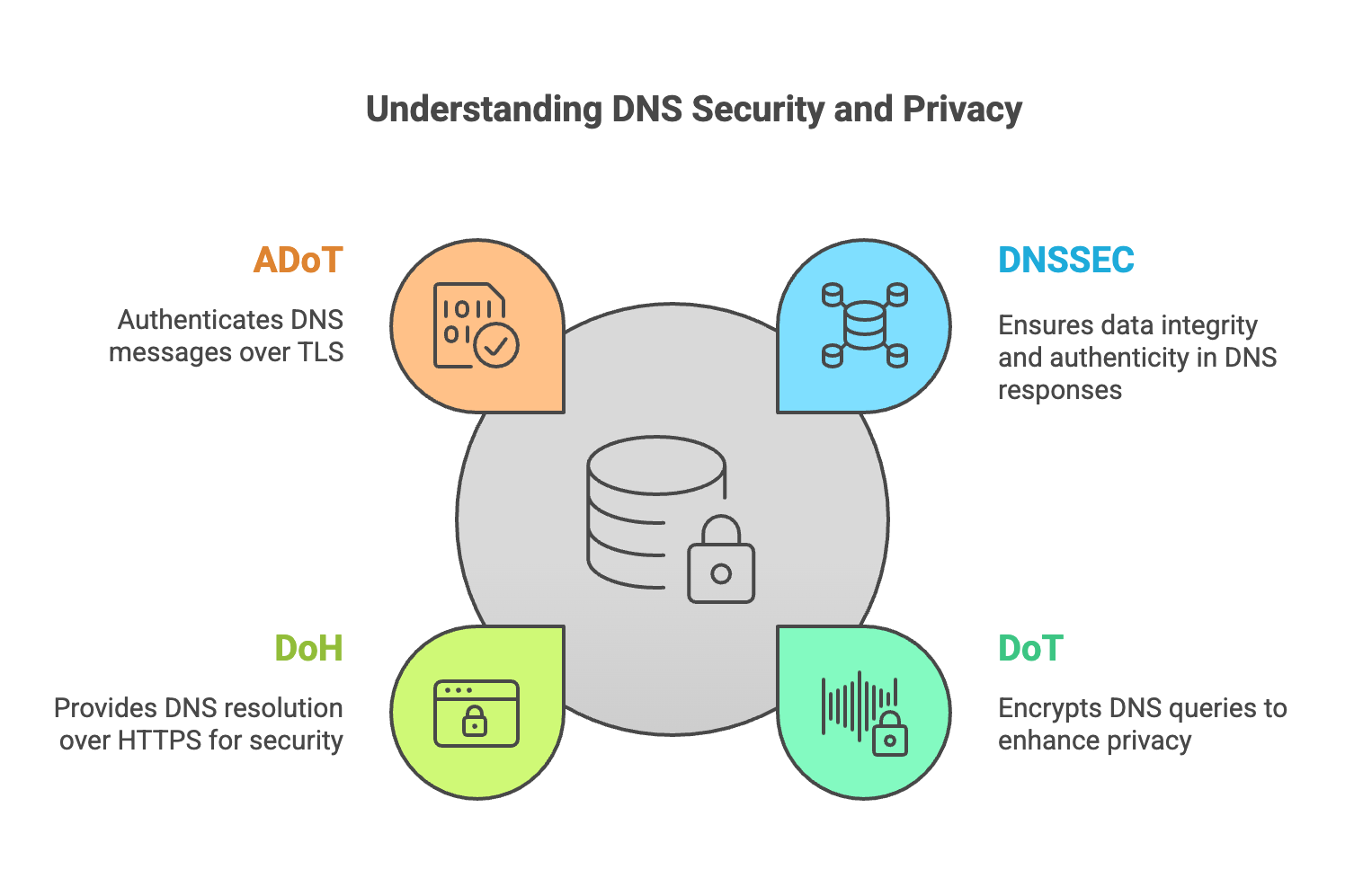
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
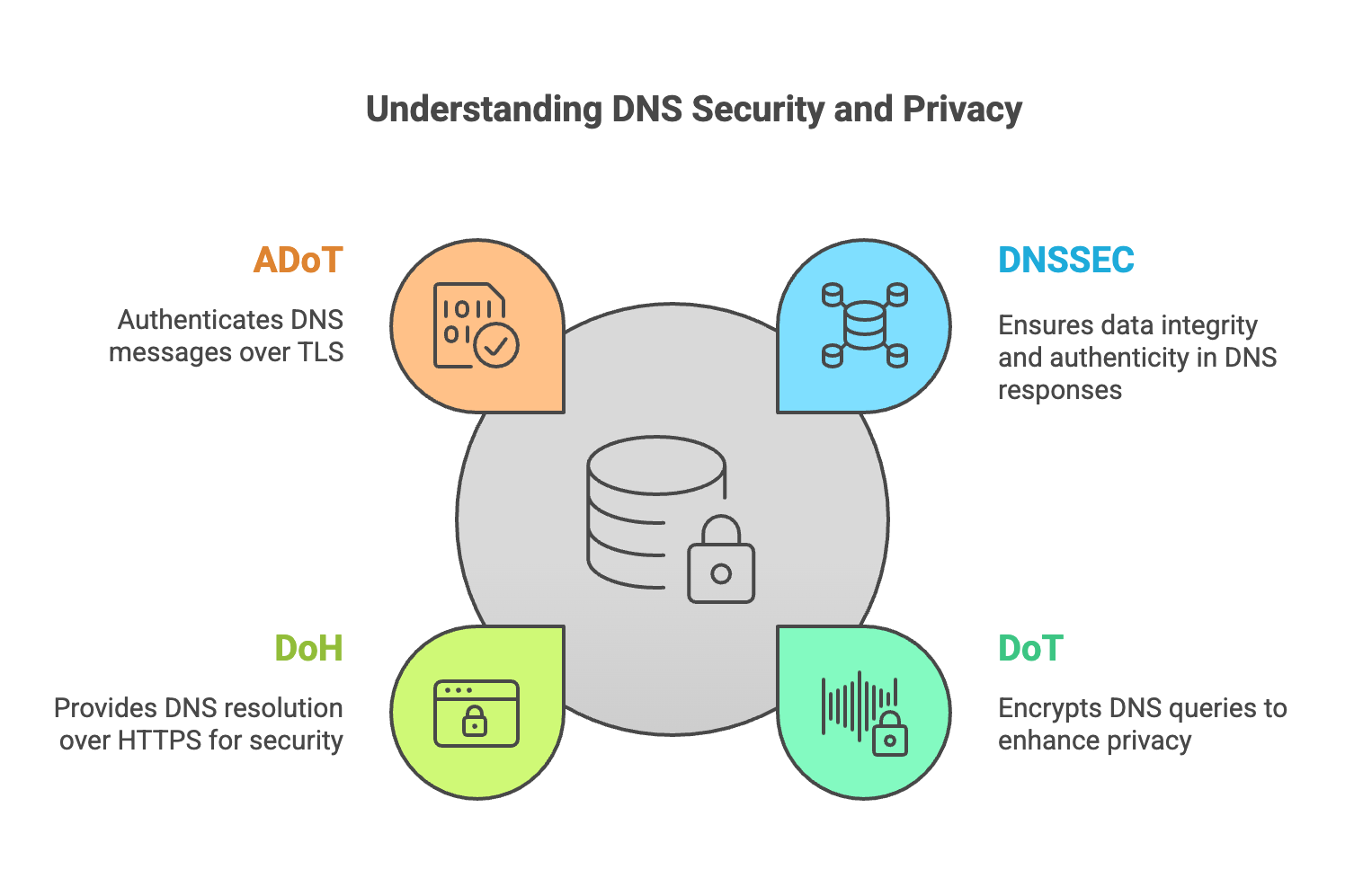
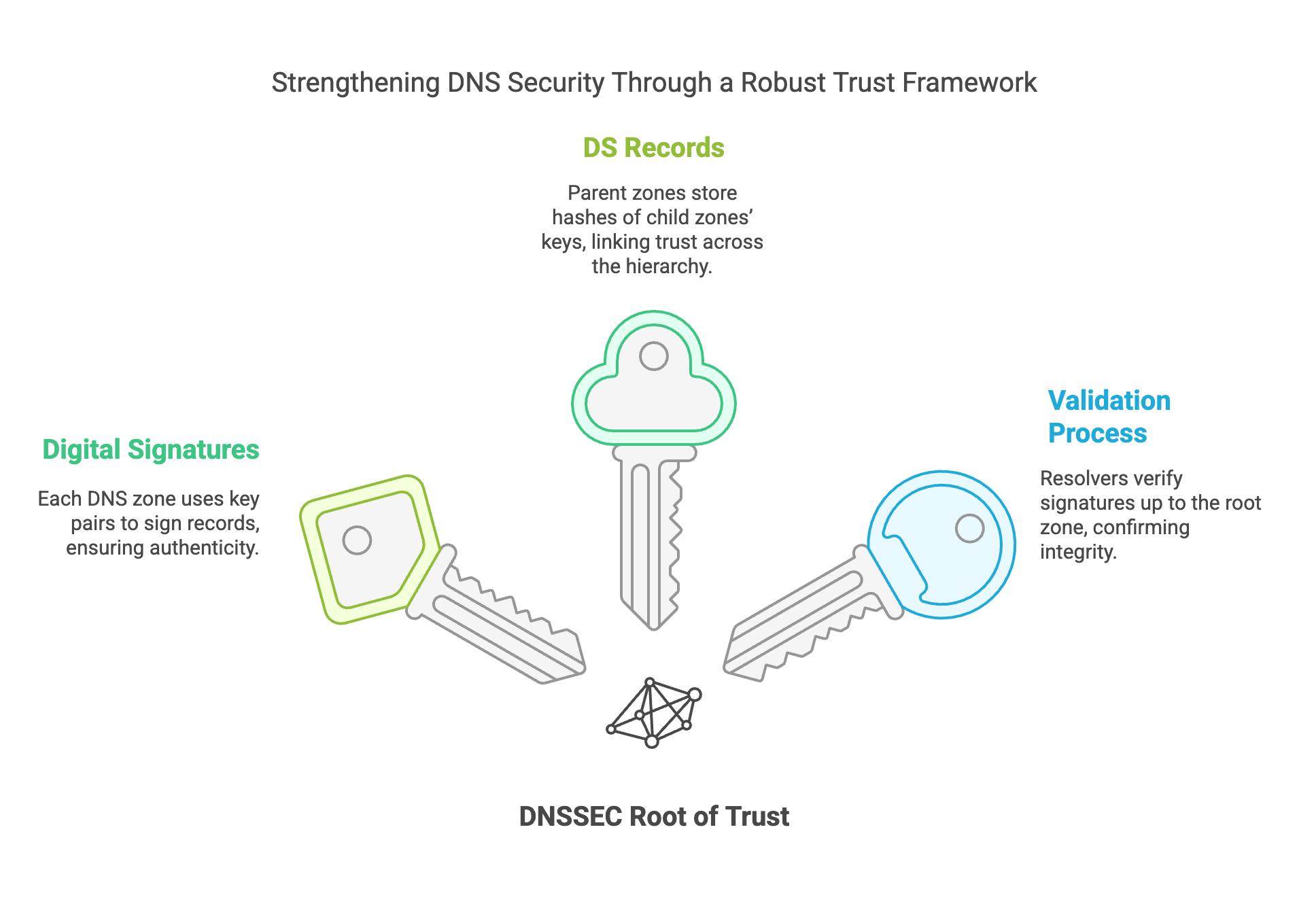
DNSSEC (Domain Name System Security Extensions) protects DNS responses from tampering by using cryptographic signatures. It ensures that DNS data received by resolvers is authentic and has not been modified in transit.
Without DNSSEC, attackers can perform DNS cache poisoning attacks that redirect users to malicious websites or phishing infrastructure.
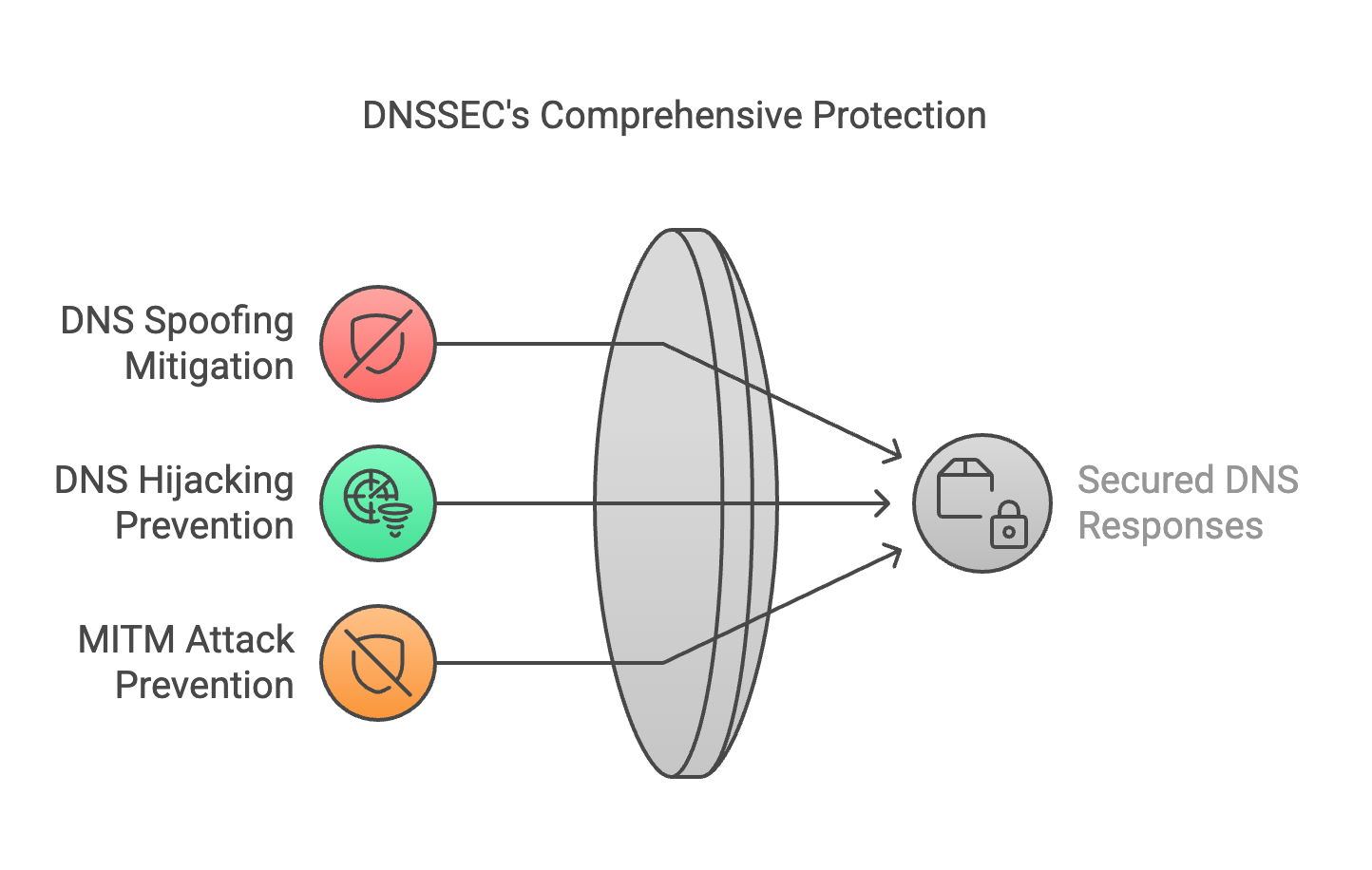
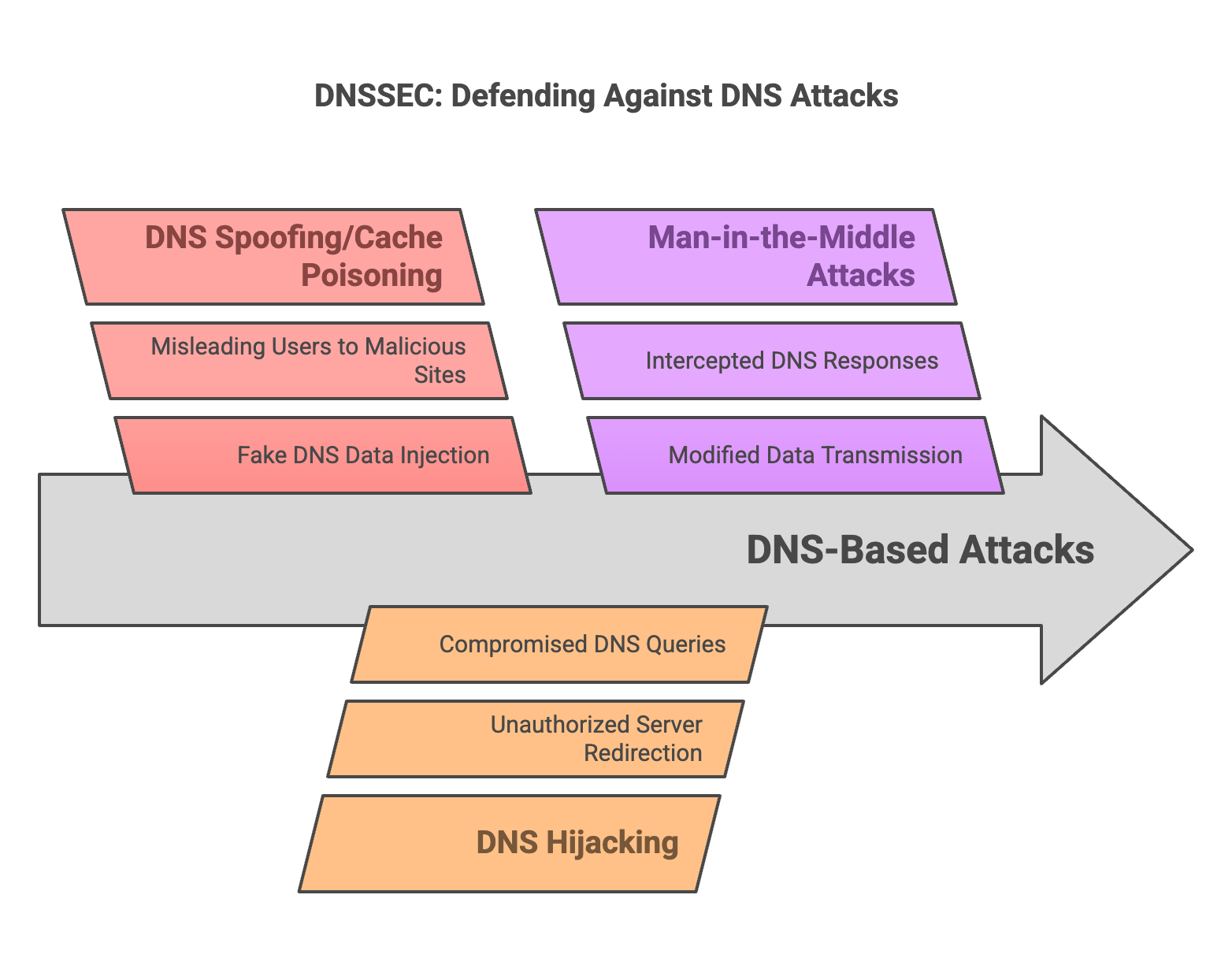
DNSSEC validation relies on a hierarchical chain of trust starting from the DNS root zone and extending through TLDs to individual domains.
The following query asks for the IPv4 address of ietf.org and requests DNSSEC data. The AD flag in the answer means the resolver validated the DNSSEC chain of trust successfully.
dig ietf.org A +dnssec
; <<>> DiG 9.18.44-1~deb12u1-Debian <<>> ietf.org A +dnssec
;; global options: +cmd
;; Got answer:
;; ->>HEADER<<- opcode: QUERY, status: NOERROR, id: 57765
;; flags: qr rd ra ad; QUERY: 1, ANSWER: 3, AUTHORITY: 0, ADDITIONAL: 1
;; OPT PSEUDOSECTION:
; EDNS: version: 0, flags: do; udp: 1232
; COOKIE: 75b195e0ab7f36520100000069ac7a4fcb810f5db831d99d (good)
;; QUESTION SECTION:
;ietf.org. IN A
;; ANSWER SECTION:
ietf.org. 300 IN A 104.16.45.99
ietf.org. 300 IN A 104.16.44.99
ietf.org. 300 IN RRSIG A 13 2 300 20260308201943 20260306181943 34505 ietf.org. MHhO/MFn0nA0iuvIeJ7XiUwfMMqhUOGwphtSF0+NLdsKKA0yCDvirGNw N+WoTT3+lXANKG97u+W0Txwu60e66w==
;; Query time: 33 msec
;; SERVER: 190.185.105.10#53(190.185.105.10) (UDP)
;; WHEN: Sat Mar 07 16:19:43 -03 2026
;; MSG SIZE rcvd: 201
In this example, the key indicators are: