ADoT Explained
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
Modern DNS security relies on a combination of integrity protection and encrypted transport protocols.
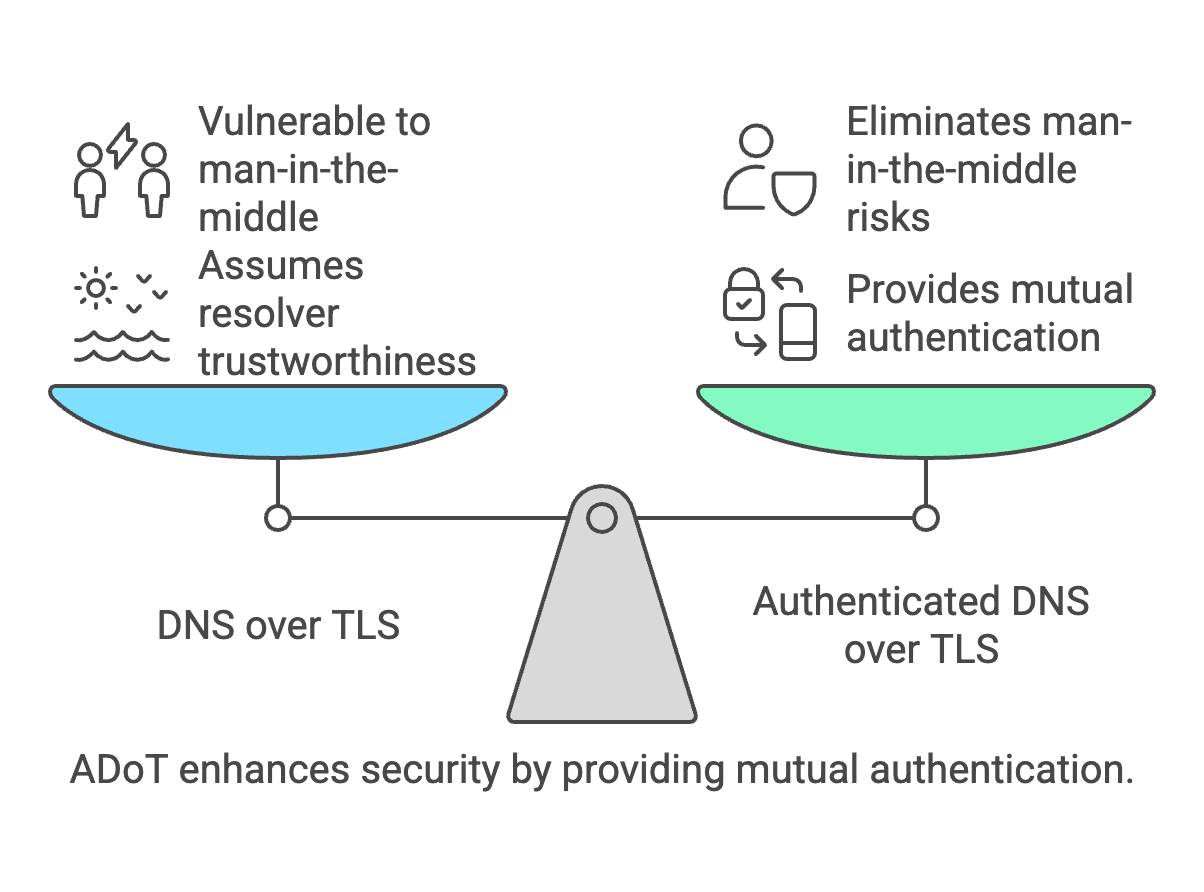
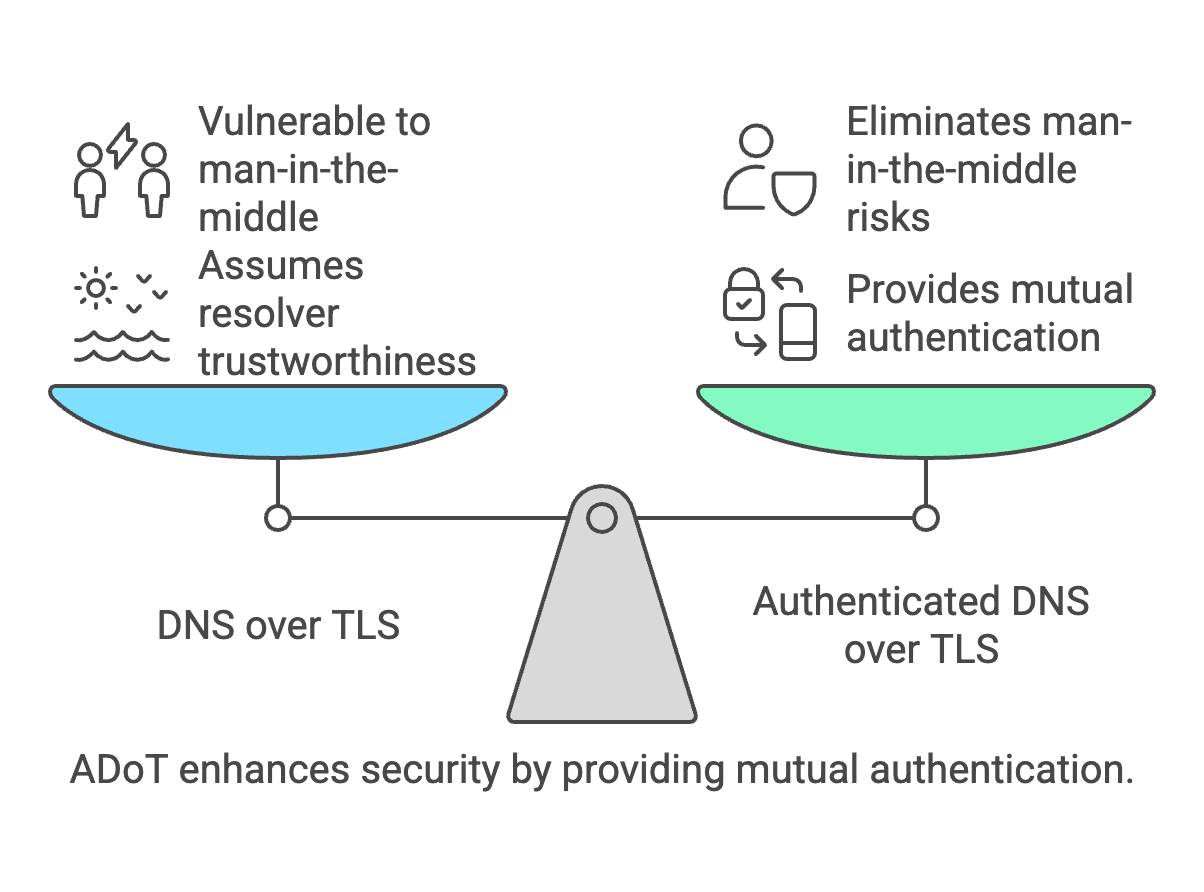
Authenticated DNS over TLS (ADoT) extends DNS over TLS by introducing mutual authentication between the DNS client and the DNS resolver. While standard DoT encrypts DNS queries, it usually assumes that the resolver is trustworthy and authenticates only the server side of the TLS connection.
ADoT adds an additional security layer by requiring both sides of the TLS connection to authenticate each other using certificates. This prevents unauthorized clients from using the resolver and protects the DNS service from impersonation or unauthorized access.
ADoT is particularly useful in controlled environments such as enterprise networks, managed endpoints, or ISP infrastructures where DNS clients must authenticate before accessing the recursive resolver.
For example, an ISP may deploy ADoT so that only authenticated customer devices can query its DNS resolvers. This allows the provider to enforce security policies, parental controls, or Protective DNS filtering while ensuring that DNS traffic remains encrypted.
ADoT deployments typically rely on mutual TLS certificates where the client presents a certificate to the resolver during the TLS handshake. If the certificate is valid and trusted, the resolver allows the DNS session.
Client → TLS handshake → Resolver
certificate exchange
mutual authentication
encrypted DNS queries