How DNSSEC Works
DNSSEC protects DNS responses using digital signatures that allow resolvers to verify that DNS data has not been modified.
DNSSEC protects DNS responses using digital signatures that allow resolvers to verify that DNS data has not been modified.
DNSSEC (Domain Name System Security Extensions) adds cryptographic signatures to DNS records so that DNS resolvers can verify that the information received from authoritative servers is authentic.
Without DNSSEC, attackers could potentially manipulate DNS responses and redirect users to malicious servers through attacks such as DNS cache poisoning.
DNSSEC prevents these attacks by allowing resolvers to verify that DNS data has not been modified during transmission.
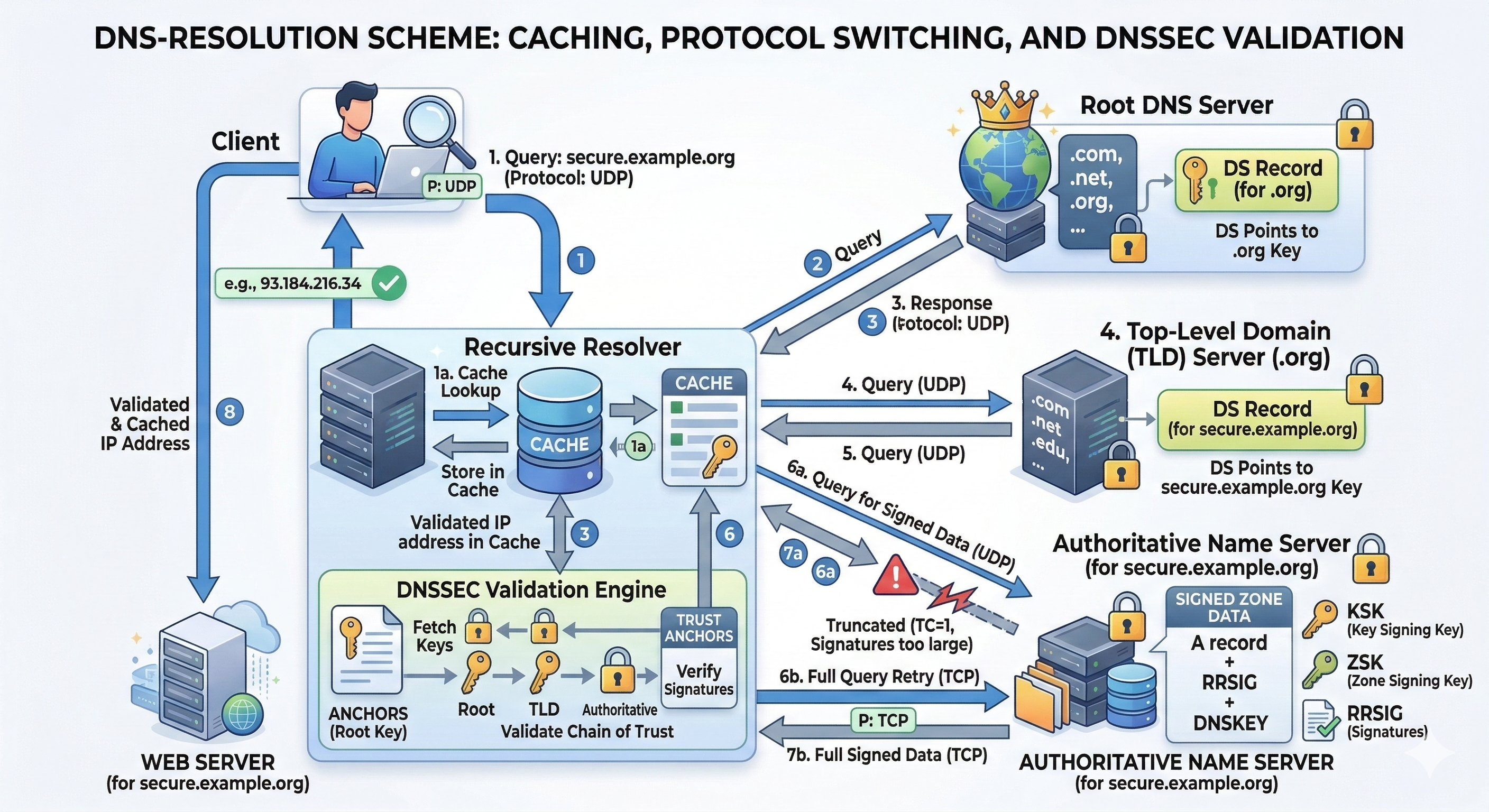
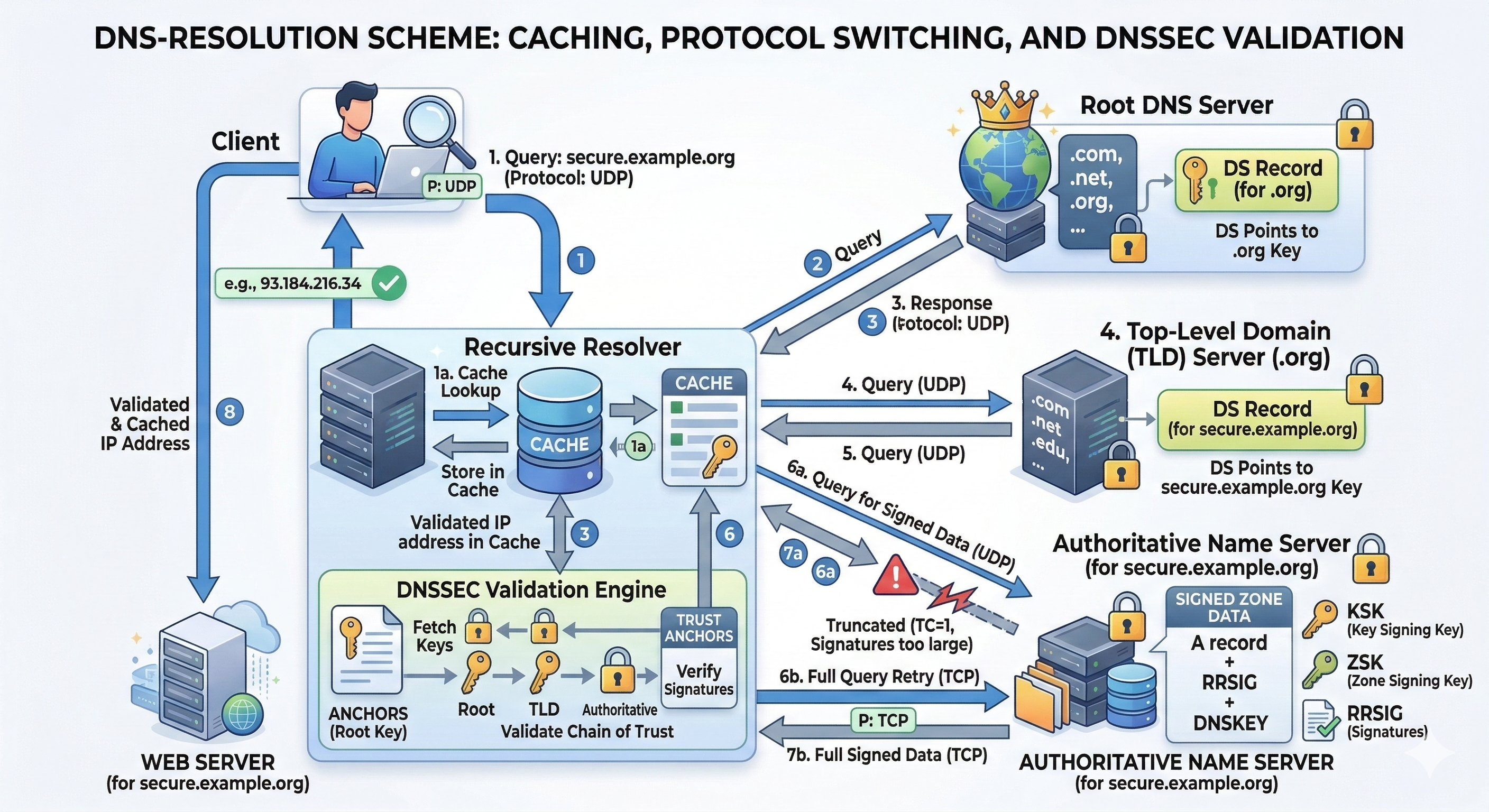
DNSSEC operates on top of the normal DNS resolution process. Queries still follow the standard DNS hierarchy:
DNS queries typically use UDP port 53, but if responses are too large (for example when DNSSEC signatures are included), the server may set the TC (Truncated) flag and the client retries using TCP.
Because DNSSEC responses are larger than traditional DNS responses, TCP fallback is more common when DNSSEC is enabled.
DNSSEC signatures are created by the authoritative DNS servers for a domain. The zone is signed using cryptographic keys.
When DNSSEC is enabled on authoritative servers such as BIND9, the server automatically generates additional records required for DNSSEC operation.
These records include:
When zone signing is enabled, BIND9 automatically creates and maintains these records when the zone is loaded or updated.
The RRSIG record contains a digital signature for a DNS record set. This signature allows resolvers to verify that the data was produced by the authoritative server and has not been altered.
The DNSKEY record contains the public keys used to verify DNSSEC signatures.
NSEC and NSEC3 records are used to prove that a domain name does not exist.
Without these records, attackers could forge negative DNS responses.
DNSSEC relies on a hierarchical trust model known as the chain of trust.
Each zone signs its own DNSKEY records, and the parent zone publishes a DS (Delegation Signer) record that references those keys.
This creates a validation chain from:
Because the root zone is trusted by DNS resolvers, this chain allows resolvers to verify the authenticity of DNS records across the entire Internet.
Recursive resolvers perform DNSSEC validation before returning DNS responses to clients.
The resolver performs the following steps:
If validation fails, the resolver returns a SERVFAIL response instead of potentially corrupted data.
DNSSEC protects Internet users and organizations from attacks that manipulate DNS responses.
It is widely used by:
DNSSEC is also an important foundation for other technologies such as DANE, which allows TLS certificates to be published and verified through DNS.