Can DNS Zone Transfers Be Encrypted?
Protecting DNS replication traffic between authoritative servers.
Protecting DNS replication traffic between authoritative servers.
A DNS zone transfer is the mechanism used by authoritative DNS servers to replicate zone data between a primary server and one or more secondary servers. This ensures that DNS records remain synchronized across multiple locations for redundancy and reliability.
Zone transfers normally occur using the following DNS operations:
These transfers are typically performed over TCP port 53. Without protection, the entire zone content may be visible to anyone able to intercept the network traffic.
Yes. Several techniques exist to protect DNS zone transfers from unauthorized access or interception.
Historically, DNS focused on authentication rather than encryption. However modern DNS infrastructure can combine multiple security mechanisms to protect zone replication traffic.
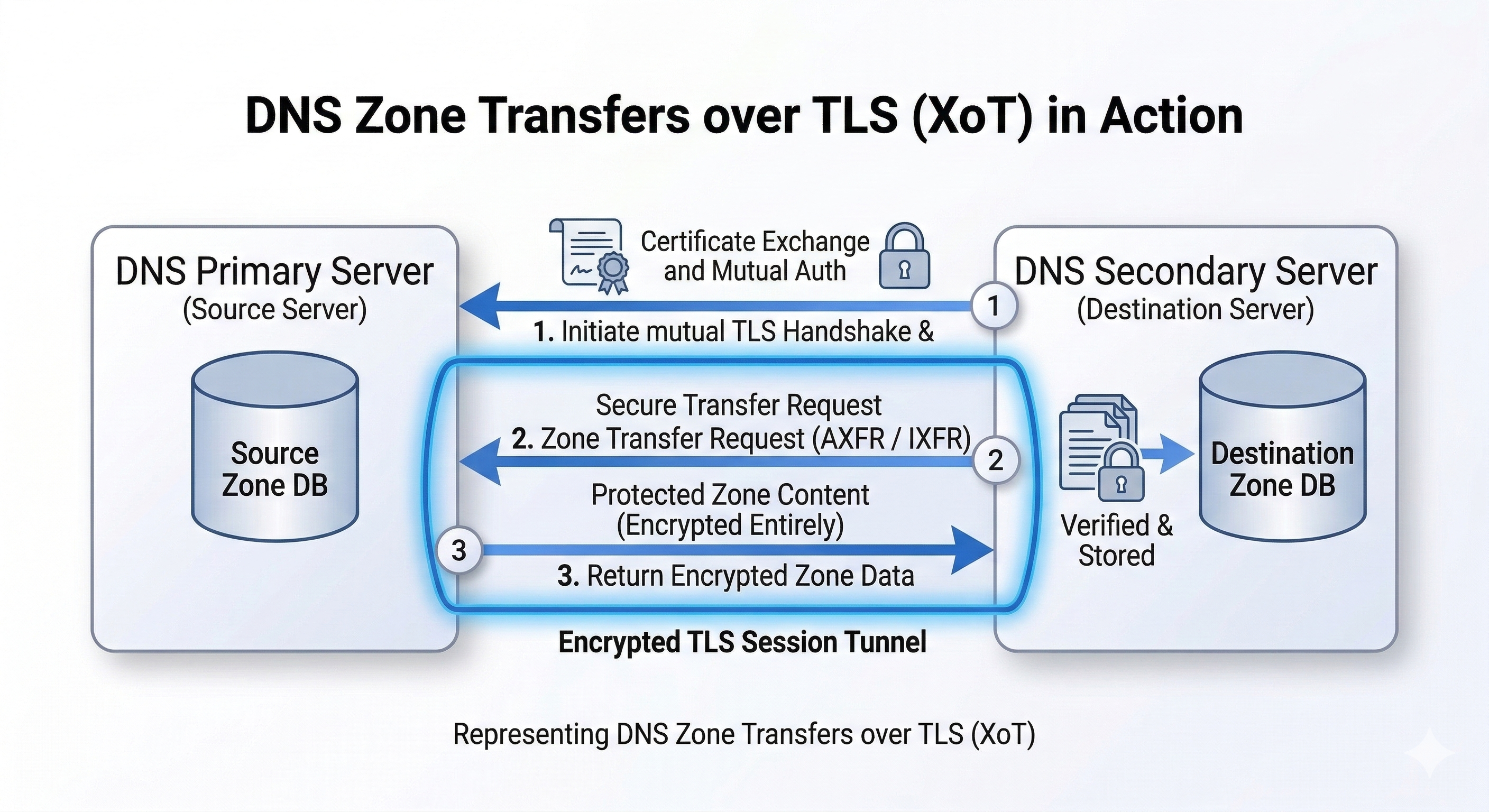
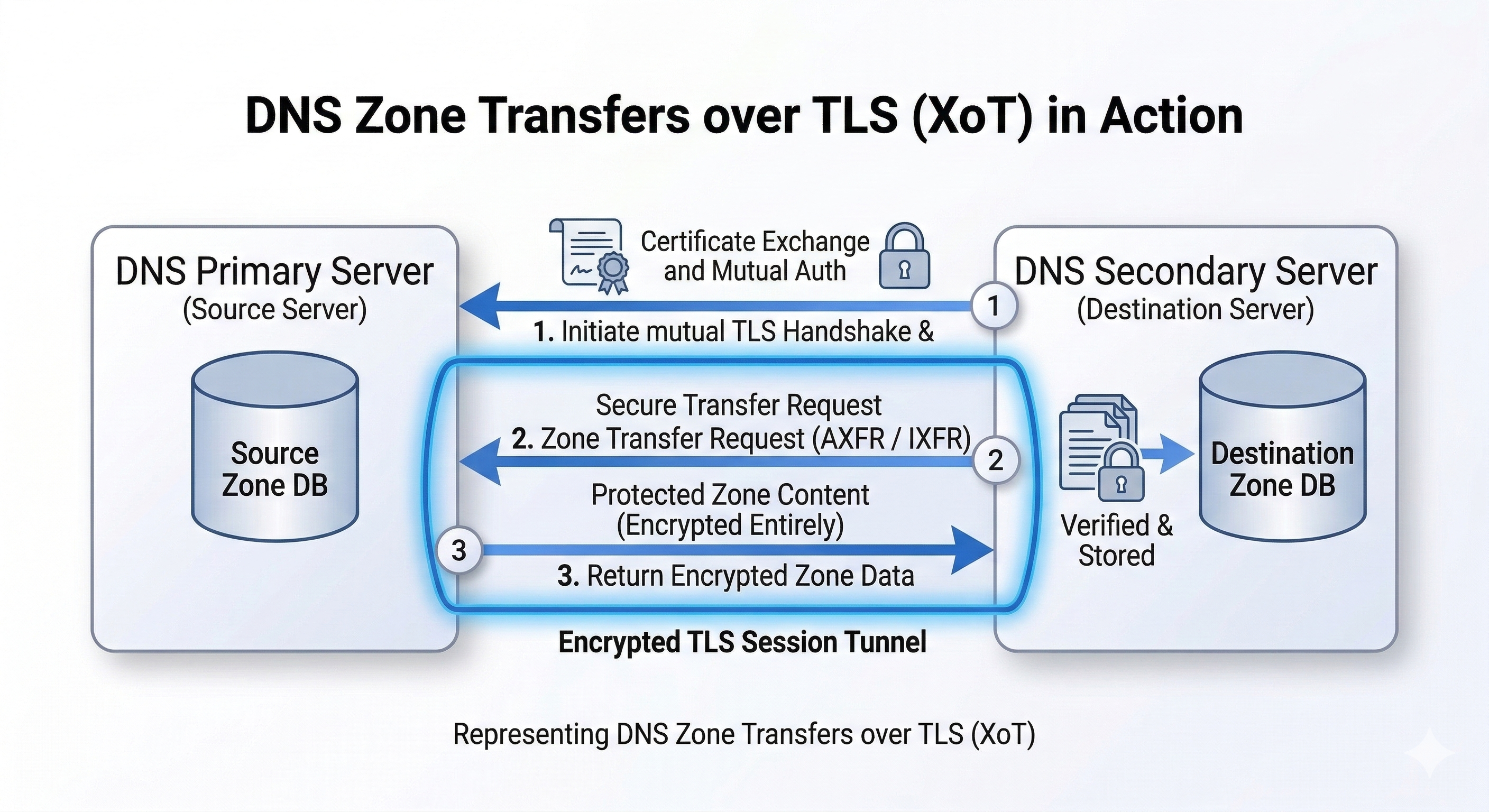
Traditional DNS zone transfers occur over TCP port 53 and are not encrypted. Modern versions of BIND9 support DNS Zone Transfer over TLS (XoT), defined in RFC 9103, which allows authoritative DNS servers to replicate zones through encrypted TLS connections.
The primary authoritative server signs the zone and allows encrypted zone transfers to the secondary server using DNS over TLS (XoT).
tls xfr_tls {
cert-file "/etc/bind/tls/server.crt";
key-file "/etc/bind/tls/server.key";
};
server 192.0.2.10 {
tls xfr_tls;
};
zone "example.com" {
type primary;
file "/var/lib/bind/db.example.com";
allow-transfer { 192.0.2.10; };
also-notify { 192.0.2.10; };
};
The secondary DNS server retrieves the zone from the primary using a TLS-encrypted connection.
tls xfr_tls {
ca-file "/etc/bind/tls/ca.pem";
};
server 192.0.2.1 {
tls xfr_tls;
};
zone "example.com" {
type secondary;
primaries {
192.0.2.1 tls xfr_tls;
};
file "/var/lib/bind/db.example.com";
};
You can verify that the zone transfer works using the dig utility.
dig AXFR example.com @ns1.example.com
When DNS Zone Transfer over TLS (XoT) is configured, the AXFR operation is performed through a TLS encrypted connection instead of a plain TCP session.
TSIG (Transaction Signature) is the most widely deployed mechanism for securing DNS zone transfers.
It uses a shared secret key between DNS servers to generate cryptographic signatures for each DNS message. This ensures that only authorized secondary servers can request zone transfers.
However, TSIG provides authentication and integrity but does not encrypt the DNS traffic itself.
A newer mechanism called XoT (DNS Zone Transfer over TLS) encrypts zone transfers using the TLS protocol.
With XoT, the AXFR or IXFR transfer occurs inside a TLS session, similar to how DNS over TLS encrypts recursive DNS queries.
XoT is supported by several modern DNS implementations including recent versions of BIND and other authoritative DNS platforms.
Many DNS operators protect zone transfers by placing authoritative servers inside a secure network tunnel such as:
In this model, the DNS servers communicate over a private encrypted network and perform zone transfers normally over TCP port 53.
This approach is common in large DNS infrastructures and managed DNS services.
If an attacker is able to perform an unauthorized zone transfer, they may obtain a complete list of DNS records for a domain.
This information can reveal internal infrastructure, mail servers, application endpoints, and other sensitive details that may assist in reconnaissance or targeted attacks.
For this reason, best practices recommend: